*A 3 minute read
Successful Distributed Denial of Service (DDoS) attacks always have the same outcome: shutting down online services, and preventing enterprises from serving their customers, employees and supply chain stakeholders.
Blindsided by an Attack
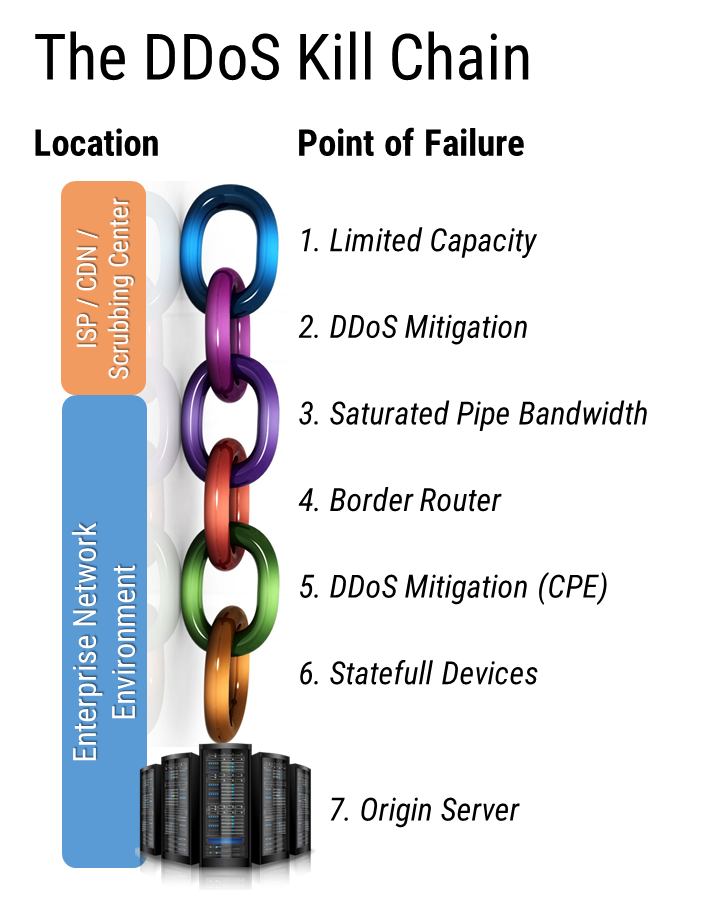
Although the outcome is always the same – downtime – protecting a network from these DDoS attacks is more complicated. This is because DDoS mitigation needs to be perfectly configured to protect against well over 100 different DDoS attack vectors traversing three OSI layers (3, 4 and 7) but also included seven different points of failure that could be responsible for the denial of service.
Take the following example:
A leading global e-commerce company was neutralized by an attack that left them dumbfounded. They had an elaborate multi-tiered DDoS mitigation posture with CDN, always-on scrubbing and cutting-edge on-premise CPE equipment with a total bandwidth of over 150 Gb. But after two hours of downtime, they still didn’t know what was keeping them offline.
We helped them understand their border router had an excessive amount of Quality of Service (QoS) features that malfunctioned when they came under attack and was responsible for their downtime.
7 Shades of Downtime
Any of the following scenarios could be explanations for the DDoS Kill Chain points of failure:
- Limited Capacity: Limited capacity at the ISP / CDN or Scrubbing Center level could result in the
respective service malfunctioning and lead to downtime.
- DDoS Mitigation: When DDoS mitigation policies are not perfectly configured to reflect the underling network, malicious DDoS traffic can leak and expose downstream network components and lead to downtime.
- Saturated Pipe Bandwidth: High bandwidth DDoS attacks (typically Layer 3 and Layer 4) could be big enough to completely saturate an enterprise’s network bandwidth and cause denial of service.
- Border Router: Enabling an excessive amount of Quality of Service (QoS) features can result in border routers that malfunction when under a DDoS attack.
- Stateful Devices: Devices such as firewalls, Web Application Firewalls (WAFs), and load balancers are not designed to process the amount of traffic caused by DDoS attacks and could malfunction, leading to denial of service.
- Origin Server: The server might be overwhelmed with requests generated by the DDoS attack and fail to serve legitimate users, resulting in denial of service.
When services are taken down by a DDoS attack understanding what needs to be fixed is anything but straightforward.
Pinpointing The Root Causes for Denial of Service
The key to breaking the DDoS Attack Kill Chain is being able to gain visibility into each point of failure’s performance and remove the root cause before the DDoS attack hits and results in downtime. Unfortunately, best-of-breed DDoS mitigation solutions don’t provide insight into the DDoS Attack Kill Chain.
Reactive solutions like ThousandEyes highlight points of failure that helps expedite detection after things go south – but they do not help understand the root cause of denial of service that could be prevented in the first place.
One needs to take a continuous approach to understand the root cause before an attack takes the network down. An approach that analyzes, discovers and strengthens the DDoS mitigation posture continuously, 24/7 and is able to close specific DDoS vulnerabilities responsible for the potential disruption. The DDoS RADAR™ is a service based on a Continuous Feedback Module that does just that.
Are Mitigation Solutions Enough to Prevent DDoS Bank attacks?
About MazeBolt
MazeBolt is an innovation leader in cybersecurity and part of the DDoS mitigation space. Offering full DDoS risk detection and elimination and working with any mitigation system to provide end to end full coverage. Supporting organizations in avoiding downtime and closing DDoS vulnerabilities before an attack happens.

 respective service malfunctioning and lead to downtime.
respective service malfunctioning and lead to downtime.

One Response
Your article helped me a lot, is there any more related content? Thanks!